All articles
The $43B Managed Security Market Is Built on a Model 84% of Security Leaders Want Agents to Replace.
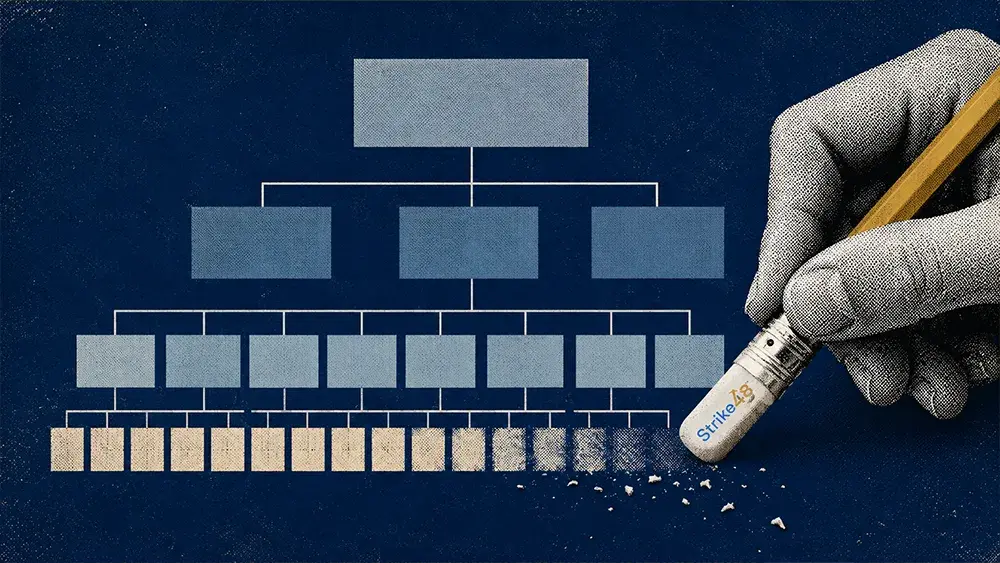
he L1 analyst tier is being quietly redesigned. Here's how leading CISOs are turning junior analysts into agent managers before the budget cycle forces it.
No security director wants to announce layoffs tied to AI. No MSSP wants to admit its staffing model is approaching obsolescence. No vendor wants to say out loud that its product replaces humans. But the budgets are being modeled, and news like Arctic Wolf's surprising 250-job cut in early May confirmed the modeling is starting to translate into tangible announcements.
Strike48's new State of Agentic Security report, based on a survey of 100 enterprise and mid-market security leaders that included 48% CISOs or Deputy CISOs, pegs the underlying calculation precisely. 84% of security leaders now agree AI agents should be doing Tier 1 work. The share willing to fully automate it: 22%. That 62-point delta is the most consequential number in security operations right now, and it's closing fast.
The math that made it inevitable
The economic case has been building for years, and the agent capabilities now arriving on the market have closed it. A typical outsourced L1 analyst costs between $45,000 and $85,000 annually all-in, and most enterprise SOCs run six to twelve of them across shifts to maintain 24/7 coverage. The managed security services market supporting that model is projected to reach $43 billion in 2026, with the majority of enterprises outsourcing at least one security function. Those analysts spend most of their time on alert triage at a rate Forrester benchmarks at around 11,000 alerts per day per SOC.
The modeling has been quietly underway across enterprise security organizations for at least two quarters. The shape that emerges across CISO conversations is consistent: a meaningful reduction in outsourced Tier 1 headcount paired with retained or expanded senior Tier 2 capacity that manages and audits agent output.
The operating model taking shape is not a fully automated SOC. It is a leaner, more senior operation: agents handle alert triage, false-positive filtering, initial enrichment, and case creation, while human analysts focus on complex investigations, threat hunting, and incident response. The Strike48 survey captures the preference cleanly. 62% of respondents somewhat agreed that L1 work should be automated, but qualified the answer by saying humans still need to stay in the loop.
The preference is reinforced by a separate finding: outsourced Tier 1 analysts at multiple enterprises are routinely abandoning alerts the moment they hit friction. The L1 layer being modeled out of the budget is often the same layer already failing to do the work being budgeted for.
Platforms like Strike48 reflect this architecture. Purpose-built micro-agents have narrow scopes of action: alert monitoring and correlation at L1, sub-agents working in parallel at L2 on patient-zero identification, historical event correlation, vulnerability mapping, and MITRE framework analysis. Full audit trails capture every action taken, and adjustable human-in-the-loop controls let security teams define exactly where agents act autonomously and where a human reviews first.
The trust crisis behind the hesitation
If the appetite is universal, why is deployment falling behind? The answer is trust. 52% of leaders cited a lack of trust in agent outputs as the top barrier to broader deployment. 41% said the technology is not yet mature enough, and 29% cited data infrastructure that cannot support effective agents.
A Deputy CISO in professional services told the survey that the bar for trust would require a vast amount of use case data showing a hallucination rate in the low single digits. The same survey found 64% of security leaders flagging three or more distinct trust concerns. The hesitation comes as a stack of overlapping objections rather than a single sticking point, and the stack is what keeps deployment running behind belief.
The data infrastructure tax
Trust in an agent's outputs is one barrier. Trust in what the agent can actually see is a second. 84% of respondents said their current tools cannot access all of their log data for investigations. 80% cite the cost of keeping log data hot as painful or a major budget concern. 65% have had at least one investigation stall in the last twelve months because the data they needed sat in a system their tools couldn't reach.
That ceiling is the practical reason 84% want agents in the SOC but only 22% are willing to fully automate. An agent inherits whatever blind spots its data layer already has, and the data layer at most enterprises is, by the SOC's own admission, partial. A recent State of SIEM Detection Risk report adds a parallel disadvantage on the rules side: the average enterprise SIEM detects only about 21% of MITRE ATT&CK techniques even on the data it does ingest. Restructuring the SOC around agents is unfinished work without solving for what those agents can see.
The training question inverts
One of the more counterintuitive implications of the report is how restructuring changes the training dynamic. In the traditional model, organizations invest heavily in training junior analysts in tool-specific workflows, only to lose that investment to turnover. With AI agents positioned to handle Tier 1 functions, the question shifts to how surviving analysts learn to manage, audit, and define the controls that govern agent behavior. The report's third recommendation makes the framing explicit: "Start training L1s to be agent managers." Whether the industry actually delivers on that reskilling promise is the open question Arctic Wolf's announcement raised first.
The security leaders who spent the last decade building out outsourced and junior-tier SOC functions are quietly designing the organizations that will replace those structures. Most are still in the modeling phase. 22% have started.
The full report is available at Strike48: State of Agentic Security: Breaking Through the Trust Barrier.